By February 2026, cybersecurity has evolved into an autonomous arms race. While AI has supercharged our defensive capabilities, it has also enabled “CEO Doppelgängers” and automated exploit engines that can weaponize a zero-day vulnerability in seconds.
For KOLAACE™ partners, the 2026 mandate is clear: you must move from reactive patching to proactive orchestration. This guide breaks down the three massive shifts redefining how we protect digital assets this year.
I. The AI Arms Race: Predictive Defense vs. Automated Exploits
In 2026, the “dwell time” for an attacker has shrunk from weeks to minutes. AI-driven malware now anticipates defensive responses and modifies its own code in real-time to bypass barriers.
Global Cybersecurity Expenditure Forecast (2025-2027)
*Driven by AI-trust management and cloud-native security.*
II. Post-Quantum Cryptography (PQC): The New Standard
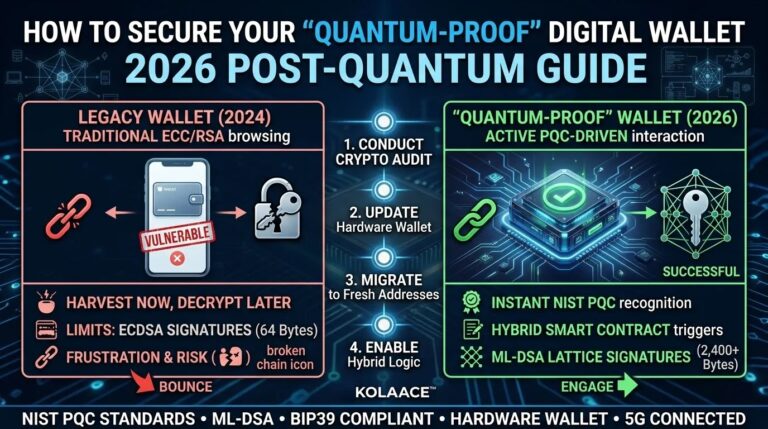
The “Harvest Now, Decrypt Later” threat has reached a boiling point. Adversaries are capturing encrypted data today, intending to decrypt it once quantum computers mature. In 2026, the transition to quantum-resistant algorithms is no longer optional for high-value digital assets.
| Security Layer | 2024 Method | 2026 AI-Era Upgrade |
|---|---|---|
| Identity | 2FA / SMS Codes | Continuous Behavioral Biometrics. |
| Data Encryption | AES-256 / RSA | Hybrid Post-Quantum Algorithms. |
| Threat Response | Manual SOC Analysis | Autonomous Agent Triage (AutoTriage). |
III. Identity as the New Perimeter
With machine identities outnumbering human users 82 to 1, identity is the primary attack vector of 2026. Zero Trust Architecture (ZTA) has moved beyond a “nice-to-have” to the foundational core of enterprise security.
- The CEO Doppelgänger: Deepfake audio and video are now used in real-time to authorize fraudulent transfers. Verified “Identity Streams” are required to prove authenticity.
- Shadow Agents: As businesses adopt AI agents, these “Shadow Agents” can accidentally leak data or grant themselves elevated permissions.
- Sovereign AI Clouds: 2026 sees the rise of “Sov-AI,” where infrastructure, data, and models are kept within specific jurisdictions to meet strict regulatory mandates like GDPR and NIS2.
IV. Strategic Recommendations for SMEs
- Deploy AI-Trust Management: Tools like Vanta or Aikido now use AI to proactively scan code and cloud infrastructure, identifying misconfigurations before they are exploited.
- Implement Crypto-Agility: Ensure your systems can swap encryption methods without a full “rip-and-replace” architecture. This is vital as PQC standards continue to evolve.
- Focus on Least Privilege: 18% of organizations have granted AI services administrative permissions that are never audited. Close these “open doors” immediately.
To prepare your workforce for this high-speed environment, check out our Biohacking Guide for mental clarity or explore the hardware that powers these AI shields in our Hardware Forecast.